Tech
How Organizations of All Sizes Can Defend Themselves Against Cyber Threats

As the number of cyber-attacks increases, organizations of all sizes need to be aware of the threat and take steps to protect themselves. Several measures can be taken to defend against cyber threats, and this article will explore some of the most effective ones. Keep reading to learn more about protecting your organization from cyber-attacks.
Understand Cyber-Threats
A cyber threat is a vulnerability in a computer system that a hacker could exploit to cause harm or damage. Some common cyber threats include malware, ransomware, phishing, and DDoS attacks. Malware is a type of software that is designed to harm or damage a computer system. It can be used to steal information, damage or delete files, or take control of a computer system. Ransomware is malware that locks users out of their computers or encrypts their files and then demands a ransom payment to unlock the computer or files.
Phishing is a scam where cybercriminals attempt to steal your personal information by sending you fake emails or messages that look like they are from legitimate sources. DDoS attacks are a type of attack where cybercriminals send many requests to a website or online service, overwhelming it and causing it to crash or become unavailable. One method organizations can use to defend themselves is by using cyber essentials vs cyber essentials plus software.
Install Software Updates and Patches Promptly


One way to protect your organization from cyber threats is to promptly install software updates and patches. Software vendors release software updates and patches to fix vulnerabilities discovered in their products. If these vulnerabilities are not fixed, they can be exploited by hackers to gain access to your systems or data. Installing software updates and patches promptly helps to close these vulnerabilities and protect your organization from cyberattacks.
In addition, it is essential to keep all of your software up-to-date, not just the software that is used to run your organization’s systems. This includes the operating system, applications, and firmware running on devices such as routers and firewalls. Software updates and patches should be tested before they are installed to ensure that they do not cause any problems with the functionality of your systems. It is also essential to create a process for installing these updates and patches so that all of your employees are aware of them and know what needs to be done to implement them successfully.
Educate Employees on Cybersecurity Risks


To defend themselves against cyber threats, organizations of all sizes should educate their employees on cybersecurity risks. Employees need to be aware of the different types of cyberattacks that are possible and how they can protect themselves and the organization’s data. Additionally, organizations should have a plan to respond to a cyberattack.
An organization’s security incident response plan (SIRP) is a document that outlines how the organization will respond to a cyber attack. The SIRP should include procedures for notifying employees, investigating the attack, and remediating any damage. The first step in creating a SIRP is identifying all potential threats and vulnerabilities. The organization should then create policies and procedures for responding to each type of threat. Employees should be trained on how to recognize and report incidents.
Restrict Email and Web Usage Policies
Email and web usage policies are essential for companies to defend themselves against cyber threats. By implementing these policies, companies can restrict employees from accessing certain websites or sending emails that could contain malware or viruses. Additionally, by having a policy in place, companies can track employee internet usage and ensure that no confidential company information is being leaked online.
Employees should be educated on the company’s email and web usage policies to understand what is allowed and is not. It is also essential for employees to be aware of the potential risks associated with clicking on links or downloading files from unknown sources. By following these simple tips, businesses can help protect themselves from cyber-attacks.


Tech
Industries that Are Great at Refreshing Older Ideas and Items


In certain industries, particularly in technology, there’s often a relentless pursuit of the newest and best ideas. Sometimes, however, the best ideas can be the ones that have come and gone, great concepts that can be refreshed and revitalized for modern times. Here are a few examples of industries that have successfully breathed new life into older ideas.
iGaming
While the online casino industry itself is relatively new, having gained popularity in the last couple of decades, the games played within it are based on formats and designs that have existed for over a hundred years. Games like blackjack and poker have been documented in some form since the early 1900s, and roulette dates back several centuries.
If you explore, for example, blackjack games at Paddy’s, however, you’ll find a lot more than just the basic game. Dozens of variations are available, as game developers have shown exceptional creativity in reimagining classics like blackjack, poker roulette, and even games like bingo and Plinko.
The iGaming industry continues to find fresh inspiration in time-tested ideas, demonstrating the potential for innovation in traditional formats.


Home Decor
Property and homes are one of the few areas where older items are often viewed as more valuable than new ones. Genuine antique furniture and decor sell for huge amounts of money, with the most expensive ones like the Badminton Chest selling for many millions of dollars at auction. With that being said, not everything brought up from the past has to be something amazingly luxurious.
A big trend right now in interior design is the idea of upcycling – taking old, decrepit, or obsolete items and transforming them into something new for the home, often with an entirely different purpose. Iconic examples include repurposing old textile machinery from factories into table bases or workbenches.
Even items like Victorian umbrella stands can be reimagined as ornamental flower vases. Upcycling demonstrates how creativity can turn forgotten objects into stylish, sustainable decor.
Fashion
Revisiting and reviving the past is something of a tradition in the world of fashion. Within the industry, it’s common knowledge that most fashions are on something of a cycle, with old styles falling out of favor and then looping back around into vogue. Every 30 or 40 years we see styles become vintage, meaning that right now the fashion trends from the 80s or 90s are a big thing again.
What many don’t realize is how far back fashion designers will go to find inspiration. Take, for instance, the ‘classical’ style that was originally worn by the Romans and Greeks over 2,000 years ago.
As recently as the 1990s and early 2000s, huge-name designers like Jean-Paul Gautier have been using Roman-inspired items in their collections. While some fashions are more niche, you won’t see a better example of renewing the old as you will in the fashion world.
The takeaway here is that no matter how much time has passed, there is always the potential to rediscover and revive great ideas from the past. With a bit of creative thinking, history can be an invaluable source of inspiration across industries. From online gaming to home decor and fashion, the old often holds the key to the new.


Tech
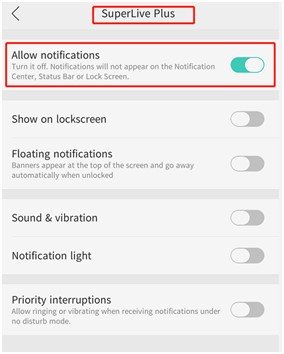
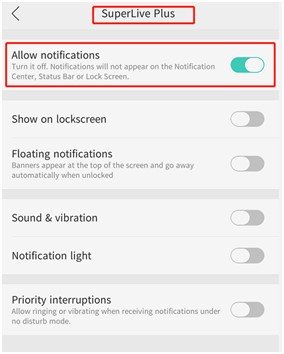
How To Download Superlive Plus For Laptop


SuperLive Plus is an app for watching security camera footage on your phone. It lets you see live video and recorded clips from cameras connected to your digital video recorder (DVR) or IP cameras.
You can control the camera’s movements, zoom in and out, and get alerts if something unusual happens. It’s perfect for business owners or anyone needing to monitor their property from anywhere.
If you prefer a bigger screen, you can use SuperLive Plus for PC. The app makes managing multiple cameras easy, ensuring you never miss important events. Whether you’re at home or on the go, SuperLive Plus keeps you connected to your security system on mobile or PC as well.
Real-time video streaming.
Do you want to see what’s happening at your place right now? The first feature of SuperLive Plus lets you watch live video from your security cameras straight on your phone. It’s like having a window to your home or business wherever you are.
Just open the app, and you can see real-time footage from your cameras. This helps you check in quickly to make sure everything is okay, whether you’re at work, on vacation, or just in another room. It’s a simple way to keep an eye on things and feel secure.
Remote playback of recorded videos.
Remote playback of recorded videos, lets you watch past footage from your security cameras on your phone. Imagine you missed something important, like a package delivery or a visitor at your door.
With this feature, you can go back and view the recorded video anytime you want, no matter where you are. You don’t need to be at home or at your business to check the recordings. It’s like having a DVR for your security cameras right in your pocket, so you can always keep an eye on things even when you’re not there.
PTZ (Pan-Tilt-Zoom) control.
One of the amazing features of SuperLive Plus is PTZ control, which stands for Pan-Tilt-Zoom. This means you can move the camera left and right (pan), up and down (tilt), and zoom in and out to get a closer look. Imagine you’re watching a live video from your security camera, and you want to see something in more detail.
With PTZ control, you can adjust the camera’s view directly from your phone. This feature helps you focus on specific areas and get a better view of what’s happening, giving you more control over your surveillance system.
Push notifications for alarms.
Ever wondered how you can know if something goes wrong without constantly watching your security cameras? The push notifications feature in SuperLive Plus does just that. It sends you instant alerts on your phone if it detects any unusual activity, like motion or sound, on your cameras.
This means you can go about your day and be aware of any potential security issues immediately. It’s like having a personal security guard who never sleeps, always ready to inform you of important events. This feature helps you respond quickly and keep your property safe.
Multiple device management.
Multiple device management, lets you connect and control many security cameras from one app. You can watch video feeds from all your cameras on your phone without switching apps. This makes it easy to keep an eye on different areas, like your home, office, or other properties, all at once. It’s super convenient because you can manage everything in one place, ensuring you stay informed about what’s happening everywhere you have a camera.
How to run Superlive Plus for PC
Using SuperLive Plus on your PC gives you a bigger screen to see details clearly, making it easier to monitor multiple cameras at once. It’s perfect for when you’re working on your computer and want to keep an eye on your security feed simultaneously.
- Download NoxPlayer: Go to the NoxPlayer website and download the emulator. It lets you run Android apps on your PC.
- Install NoxPlayer: Open the downloaded file and follow the instructions to install NoxPlayer on your computer.
- Launch NoxPlayer: After installation, open NoxPlayer. It will look like an Android phone on your PC.
- Sign in to Google Play: In NoxPlayer, open the Google Play Store and sign in with your Google account.
- Search for the app: Type “SuperLive Plus” in the search bar and press Enter.
- Install the app: Click the app in the search results and press “Install.”
- Open the app: Once installed, find the app on the NoxPlayer home screen and click it to start using SuperLive Plus for PC.
Tech
Portrait Photography Techniques: Creating Expressive Images


Creating expressive portraits requires not only the ability to handle the camera but also an understanding of psychology and working with the model. Portrait is the art of capturing not only a person’s appearance but also their emotions, character, and personality.
Importance of light
Light is very important for creating the atmosphere and therefore the expressiveness of a portrait in several aspects at once.
- Light determines the shape, texture, and volume of an object, in this case, the model’s face.
- The right lighting will help to emphasize the best features of the face and hide flaws. If the camera still “noticed” some defects, you can remove them in the process of retouching. For example, if you want to get a smooth skin app Retouchme will fix the photo in a couple of clicks.
- Lighting effects and shadows can be used to create emotionally rich portraits. Soft lighting can create a gentle and romantic mood, while harsh shadows add drama and intrigue.
If you choose to shoot in natural light, avoid high sun: it gives harsh shadows. The optimal time to work is the photographer’s golden hour. If the day is cloudy, the light will be soft and diffused, so you can shoot even at noon.
Studio portrait photography uses softboxes, light panels, and reflectors to control the direction and intensity of the flow. Professional lighting is usually more predictable and controllable, so the photographer will be able to create the effects they want and adjust their work on the fly.
Flashes when shooting a model help create bright contrasting portraits and are also used to soften shadows when working with natural light.
Composition and angle
For a model to “read” well in the frame, you need to think about the position of the face and the direction of the lens. What basic techniques does the photographer rely on?
1. Rule of thirds.
Divide the frame into nine equal parts. Position the main subject (in this case, the model’s face) near the intersection of the lines.
2. Diagonal lines.
Use diagonal lines in your composition to direct the viewer’s eye toward the face. Position the model so that the eye line tends to run along the diagonal line.
3. Positioning the main object.
Place the main subject (the face) in the center of the frame – this is how you get a confident and focused image. Use the golden ratio by positioning the model on one of the lines to achieve a balance between the main object and the space around it.
4. Use of negative space.
Leave enough space around the model’s face to create a sense of “breathing” and depth.
5. Work with foreshortening.
Experiment with shooting directions, such as a high or low angle.
6. Use background.
Include prominent details such as trees or architecture to create an interesting background. Use surrounding elements as a frame for the model’s face to draw attention to the main subject of the portrait.
These tips will help you shoot expressive portraits just by working with composition alone.
Creative angles: unconventional approaches to portraiture
Experiment with blurred backgrounds or using macro photography to create unconventional effects in portraits. This can help highlight the main subject and add dynamics to the image.
- Use mirrored or reflective surfaces (glass, water, metal) to create unique effects in portraits.
- Try using the model’s movement while shooting by setting a slow shutter speed.
- Use aerial platforms, drones or other devices to get unconventional angles from above or below.
Is the background important for an expressive image?
The choice of surroundings plays a key role in creating the overall image that the viewer will see. Here are a few techniques that will add just the right amount of expression to your images.
- Try to achieve contrast between the background and the model’s face or, conversely, create harmony by using complementary colors and textures.
- Take into account the style and character of the portrait. For example, use natural surroundings if you want to achieve a calm image, or add abstract details for a non-basic role.
- Match the background to the mood you want to convey, such as light and bright colors for a joyful and optimistic portrait or darker tones for a mysterious and dramatic mood.
- A minimalistic background, such as a solid-colored wall, will focus the viewer’s attention on the model’s face. A rich environment with interesting objects and textures will set the mood before the camera is even turned on.
As you can see, the right choice of frame filling will enhance the expressiveness of the portrait and emphasize its character.
Shooting portraits is not just a process of creating images, it is an opportunity to see the moments of life, to express the individuality and uniqueness of each person. With the right techniques, the photographer captures images that will inspire.



 Work12 months ago
Work12 months agoFrom Rookie to Veteran: Navigating the Career Path of a Long-Distance Trucker



 Entertainment12 months ago
Entertainment12 months agoUnderstanding the Difference Between Probability and Odds



 LifeStyle12 months ago
LifeStyle12 months agoGrandparents Thriving in Senior Living Communities



 E-Commerce12 months ago
E-Commerce12 months agoDropshipping in 2023: Trends and Innovations to Stay Ahead in E-Commerce



 Tech12 months ago
Tech12 months agoA Comprehensive Guide to Bubble Chart Design Principles and Best Practices



 Business12 months ago
Business12 months agoHow Professional Translation Services Connect Businesses and Clients Worldwide



 Home Improvement11 months ago
Home Improvement11 months agoWhat Are the Most Common Roof Types?



 Beauty12 months ago
Beauty12 months agoHow to Choose the Right Shampoo for Your Hair Type














